The basic premise behind encryption is that it offers effectively unbreakable security. There is simply no practical way to overcome strong encryption without the existence of a “backdoor” that allows one to obtain the decryption keys. The secret sauce behind unbreakable encryption is a numerical puzzle so incomprehensibly difficult that even the fastest computer would have no hope of solving it, not even if given (quite literally) a million billion years to run. However, that presumption of impossibility has now been shattered by the advent of quantum computing.
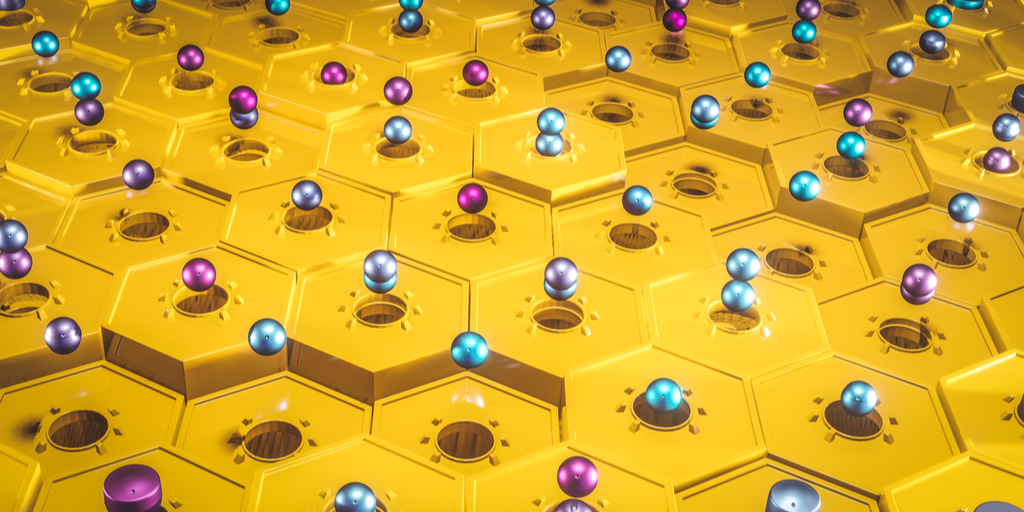
Quantum computers are fundamentally different from classical computers. Traditional computer transistors can take a value of either 1 or 0, on or off, to store one “bit” of information. Quantum computers instead use “qubits” that can assume a value of 1, 0, or any value in between. This allows qubits to counterintuitively be partly on and partly off at the same moment, a property called “superposition.” Superposition dramatically expands the number of possible different configurations that an arrangement of qubits can take, thereby amplifying their computational potential by a dizzying amount.
Qubits also make use of a phenomenon called “quantum entanglement.” Einstein called this “spooky action at a distance,” but in the ordinary sense this just means that entangled qubits are able to affect one another without necessarily being in physical contact. An operation or measurement performed on one entangled qubit will have a predictable impact on all other entangled qubits. A quantum computer exploits this relationship by entangling multiple qubits so that a collection of entangled qubits together stores all of the possible combinations of states that the computer system can assume.
As a consequence of these properties, quantum computers can dramatically outperform classical computers. While a classical computer’s problem-solving power scales linearly with the volume of computing power available to it, quantum computers operate on a geometric scale. For instance, a doubly difficult problem will take a traditional computer twice as long to solve, but it will only take a quantum computer √2 as long, or 41% longer. This may not sound like much of a difference, but the time savings add up when the problems get much harder. All things being equal, when dealing with a problem a million times harder, it will take a traditional computer a million times longer to solve it…but for a quantum computer, only a thousand times longer.
To illustrate the potential difference this could make, a 2048-bit SSL certificate would take an average desktop computer about 6.4 quadrillion years to crack.[1] But Martin Ekerå at the KTH Royal Institute of Technology in Stockholm, Sweden and Craig Gidney of Google have shown that a quantum computer with 20 million qubits could theoretically solve it in only about 8 hours.[2]
Quantum computing has been the stuff of science fiction for decades, but recent breakthroughs are now dramatically accelerating the timeline for quantum computing to go from concept to reality. Not long ago, experts assumed it would be decades before the first quantum computers would be built, but a 72-qubit quantum computer is now already operational.[3] Even more astonishingly, a paper last month stunned the world by revealing that Google has successfully used a 54-qubit quantum computer called Sycamore to complete a computation in just a few minutes that would have required over 10,000 years for the world’s fastest supercomputer to complete – an achievement that has been widely referred to “quantum supremacy.”[4] Encryption enthusiasts predicted with glee that a quantum computer like Sycamore could potentially pack enough computing power to mine all 3 million remaining Bitcoins in about 2 seconds (bitcoins are designed to be mined at a rate of 12.5 globally every 10 minutes).[5] But IBM, another leading name in quantum computing research, has questioned the accuracy of Google’s claim, estimating that its Summit classical supercomputer could actually run the calculation in as little as 2.5 days.[6]
Even if Google’s achievement falls short of true quantum supremacy, that milestone is in any case still far closer than previously thought. While 72 bits may seem like a far cry from 20 million, consider the fact that computers in the 1970s contained only thousands of transistors, while today’s latest processors can pack billions onto a chip the size of a fingernail.[7]
There do exist post-quantum codes to encrypt information so that even a quantum computer will not be able to crack it. However, these encryption algorithms are rather unwieldy – for example, one post-quantum encryption algorithm requires the use of a public key with a file size weighing in at over a terabyte.[8] One can imagine the huge expenses and logistical challenges associated with rolling out this type of encryption on a wider scale. It might only make sense to use post-quantum encryption algorithms for critical information that needs to be kept secure for very long periods of time; longer than the 20-25 years it may take for quantum computing technology to advance.
Quantum computers are still in their infancy, but the technology is developing at a rapid and accelerating pace. Records managers and IT admins would do well to start thinking about employing post-quantum encryption for the most vital records and information that require long-term protection, lest they be caught unprepared once quantum computing technology eventually takes off. The consequences are trivial if an encrypted email about a new marketing initiative or an instant message about grabbing tacos for lunch might be decrypted 20 years from now. But for highly sensitive information – e.g., candid or embarrassing high-level conversations of top executives or government officials, classified top-secret documents, the formula for Coke – one may care very much about that information being potentially exposed a few years down the road.
While most companies do not possess information that rises to this level of sensitivity, those that do need to be clear-eyed about the potential future implications of quantum technology and take proportional measures to prepare for its arrival. A “wait-and-see” approach is often a wise choice in the records and information management space when dealing with potential legal, regulatory, or technological developments. But when hardening critical systems against quantum computing attacks, time may be a luxury that one can ill afford, and the failure to make necessary preparations well in advance of quantum computing technology developments could potentially have disastrous consequences for the security of vital information.
[1] https://www.digicert.com/TimeTravel/math.htm
[2] https://www.technologyreview.com/s/613596/how-a-quantum-computer-could-break-2048-bit-rsa-encryption-in-8-hours/
[3] https://www.sciencenews.org/article/google-moves-toward-quantum-supremacy-72-qubit-computer
[4] https://www.newscientist.com/article/2217347-google-claims-it-has-finally-reached-quantum-supremacy/
[5] https://bitcoinist.com/3-million-bitcoin-in-2-seconds-google-quantum-computer/
[6] https://hexus.net/tech/news/cpu/136028-ibm-disputes-googles-quantum-supremacy-claim/
[7] https://www.sciencealert.com/new-computer-chips-can-fit-30-million-transistors-on-your-fingertip
[8] https://eprint.iacr.org/2017/351.pdf
Disclaimer: The purpose of this post is to provide general education on Information Governance topics. The statements are informational only and do not constitute legal advice. If you have specific questions regarding the application of the law to your business activities, you should seek the advice of your legal counsel.

Author: Frank Fazzio, IGP, CRM
Analyst / Licensed Attorney